Sign up for our free newsletter
Subscribe to the Mother Jones Daily to have our top stories delivered directly to your inbox.
By signing up, you agree to our privacy policy and terms of use, and to receive messages from Mother Jones and our partners.
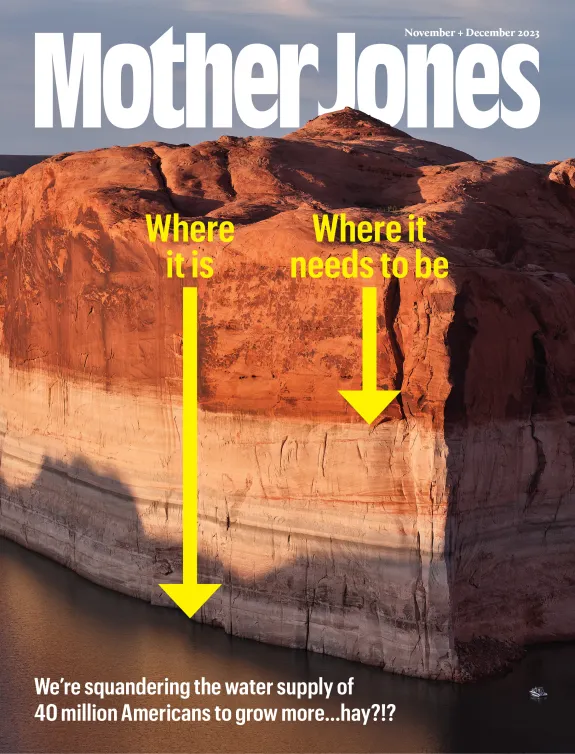
Get our award-winning magazine
Save big on a full year of investigations, ideas, and insights.
Subscribe