Reporters/Zuma
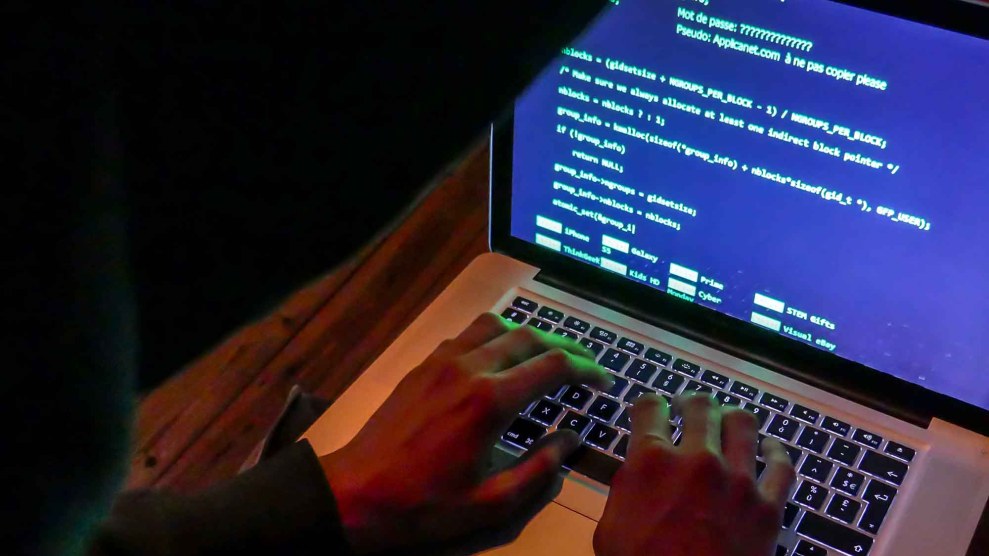
Last weekend at the DEF CON conference—the annual get together for hackers, spooks, and computer enthusiasts—hackers showed how easily voting machines could be hacked, proving once more how vulnerable they are to cyber attacks. But conference organizers did not restrict the electoral hacking demonstration to voting machines. A virtual voter registration data base was also attacked, and defended, which experts say is just as worrisome.
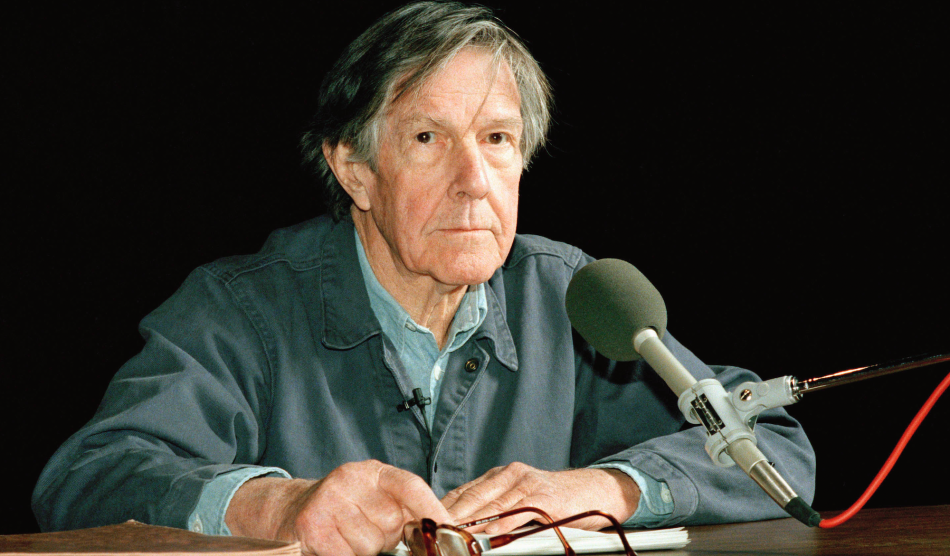
“If you look at all of the reports about foreign actors, malicious actors attacking US election infrastructure in the last election, they were not attacking the election machines,” Harri Hursti, an expert in hacking voting machines, and one of the co-organizers of the voting machine hacking exercises, tells Mother Jones. “They were attacking the back-end network, the underlying infrastructure. This was the simulation that showed how vulnerable [it is] and how hard it is to defend.”
State voter registration databases contain information about every registered voter in the state, as required by federal law. The information varies by state, but typically includes a voter’s name, date of birth, party registration, address, and, perhaps, social security number. Modifying or deleting parts of that data could, in theory, prevent someone from casting a ballot or, at the very least, delay voter check-in on site. Delays can exacerbate already long lines in some places, which may cause some people not to vote at all.
In the months since the US government formally accused hackers working with, or for, the Russian government of meddling in the 2016 US presidential election, there have also been allegations that hackers probed state election registration databases across the country. In June, Bloomberg Politics reported that state election databases in 39 states were “hit” by Russian hackers—although the exact meaning of the word “hit” is unclear in this context. State election officials in Illinois found evidence that hackers had “tried to delete or alter voter data,” and data on roughly 90,000 voters was downloaded by the attackers.
A subsequent Time story reported that the probing of state election systems was so severe in 2016 that the Obama administration had drawn up a 15-page contingency plan in case hackers tried to interfere with election infrastructure on election day by doing things such as messing with voter registration records to gum up poll stations or shutting down the machines themselves.
The annual DEF CON hackers conference in Las Vegas is one of the premier annual events for hackers from around the world to gather and review the most up-to-date information on security, hacking, computer exploits, and the like. This year, organizers set up what they called the “Voting Village,” where they let hackers attempt to hack voting machines that were obtained via eBay. Hackers were able to compromise many of the systems without considerable effort—one 16-year-old hacked a machine in about 45 minutes.
“The current generation of voting technology used in the US has, since its introduction after the turn of the century, enjoyed something of a ‘honeymoon’ from serious attack up until now,” Matt Blaze, a University of Pennsylvania professor and co-organizer of the DEF CON hacking exercise, wrote recently in his blog, after The Intercept published a classified NSA document detailing alleged Russian attempts to access the networks of election infrastructure suppliers in the US. “It’s abundantly clear,” he continued, “that the honeymoon is over.”
Until relatively recently staging an event where voting machines were hacked would have been illegal, which left only a few security researchers able to test voting machine security. In 2015, the law was changed and part of the change concerned circumventing software designed to restrict access to copyrighted material. That meant that this year organizers were able to allow hackers access to the used machines.
Hackers testing the security of 30 voting machines at Defcon
“We got in within 35 minutes” pic.twitter.com/Zc9cKBXpD4#defcon #Defcon25 @defcon— Matthijs Pontier (@Matthijs85) July 29, 2017
Hursti, the Finnish founder of Nordic Innovation Labs, a cyber security firm, says observers included state election officials and staff from the Department of Homeland Security, the federal agency that says its offers to help secure state systems before the elections had been rebuffed by state election officials. A DHS spokesman tells Mother Jones that several dozen “mostly mid-level cyber-analysts” who work at DHS attended DEF CON; they may have watched the demonstration but had no active role in organizing the event.
Organizers also created a “cyber range,” made up of computer servers onto which they loaded simulations of a real voter registration database. To insure that it was “as realistic as possible,” an election official “from a very large and important jurisdiction who chose not to be identified,” helped out, Hursti says.
The organizers then asked hackers to either attack the network as part of the “red team,” or try to defend the network in real time from those attacks as part of the “blue team,” an exercise common in the cyber-security world. Attackers were able to penetrate the virtual system, which, in a real-life setting, would allow them to perhaps manipulate voter registration rolls or delete data. The exercise demonstrated how challenging it is to defend voter registration systems, and, most importantly, how under-trained and badly prepared state and local officials tasked with defending those networks are.
“In a lot of these offices you don’t have a single person doing security,” Hursti says. “You have a guy who is running the network, and he is supposed to do the security too and also look through servers. That is incomprehensible because the people who have that kind of skill set are so scarce … the fortress is undefended in many cases.”
Hursti and several others are attempting to create more organized training for state and local computer network employees so they can learn more about how to defend their election systems. In the meantime, he says, officials should keep an eye out for tried and true computer network breach tactics like spear phishing, where a targeted employee with access to the network clicks on a link or attachment in an email, giving attackers access to the network. Spear phishing is a common and relatively basic tactic for attackers to gain access to computers—it is believed that Hillary Clinton campaign chairman John Podesta’s email account was breached after a successful spear phishing attack.
“The same attacks that worked 30 years ago work today because they also rely on the vulnerability of the humans,” Hursti says. “You send a cute kitty picture or a cute dog picture, and people do click it. Then the game is over.”
Blaze touched on spear phishing as a tactic. “Targeted phishing attacks and malware hidden in email attachments might not seem like the kind of high-tech spy tools we associate with sophisticated intelligence agencies like Russia’s GRU,” he wrote. “They’re familiar annoyances to almost anyone with an email account. And yet they can serve as devastatingly effective entry points into even very sensitive systems and networks.”
In June, during his testimony about Russian meddling in the 2016 presidential election to the Senate Intelligence Committee, former FBI Director James Comey predicted that Russians are not done tampering with election systems. “They’re coming after America,” he said. “They will be back.”
Hursti says that Comey’s ominous take may have been optimistic.
“They are not going to come back,” he says, “because they are not leaving.”