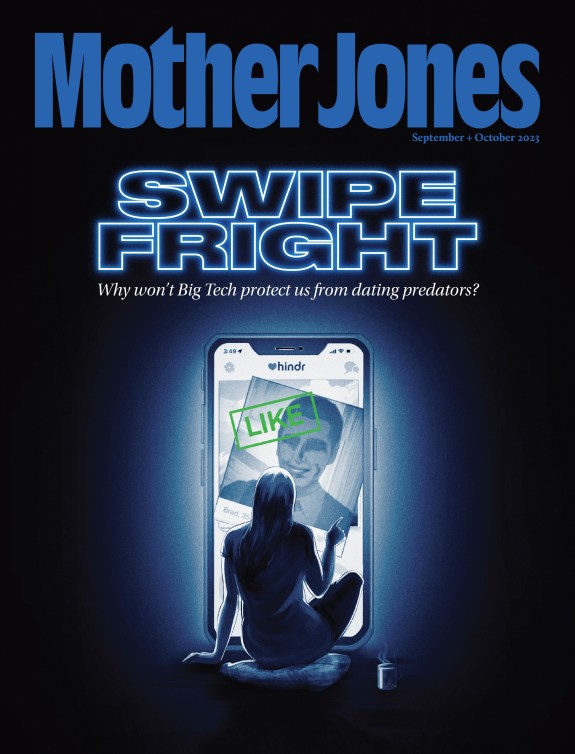
Photoillustration by Ivylise SimonesCreatas/Thinkstock; da-vooda/Thinkstock
On Sunday, the Washington Post published an exposé revealing that private companies are peddling surveillance systems to foreign governments that track the location of cellphone users in the United States and abroad. The report raised a basic question: How can this be happening when cellphone companies generally promise not to disclose their customers’ location information without their consent? The main problem is that location information is available on a global network that can be accessed by thousands of companies. And in the wake of the Post story, US cellphone companies are refusing to discuss how this squares with their privacy policies, or say what they are doing to keep their customers’ whereabouts confidential.
Here’s what’s going on: Carriers collect location information from cellphone towers and share it with each other through a global network called SS7. This allows a US carrier to find a customer even if she hops a plane to India. But according to the Post, surveillance systems makers have gained access to SS7 and are using it to grab location data, allowing these firms to pinpoint people within a few city blocks.
It’s not clear how private surveillance companies have obtained access to the network. Major cell carriers sell SS7 access to other providers, as do third-party companies. Karsten Nohl, a cryptographer and telecommunications researcher based in Berlin, says that these players, some of their business partners, and “anybody hacking any of the above” can send and receive SS7 messages. Albert Gidari Jr., an attorney at Perkins Cole who specializes in privacy and technology, says that it’s likely that a surveillance company could get access by representing itself as a provider.
Verizon, Sprint, T-Mobile, and AT&T each promise their customers that their location is protected (with exceptions for emergencies and complying with court orders). AT&T’s privacy policy states, “We’ll give you prior notice and ask for your consent when your location is used or shared.” Verizon’s reads, “Verizon Wireless services that use mobile device location data provide you with notice about the collection and use of this data.” Sprint and T-Mobile make similar promises, although some of these companies include the caveat that they cannot protect data that is collected by third parties while a customer’s phone is roaming.
Mother Jones asked each of these firms whether it has knowingly granted location data to surveillance companies and what it is doing to protect consumer location data to meet the promise of its privacy policies. Not one would comment.
Carriers can modify their systems to choose to share location data only with trusted companies. The Post reports that carriers have some ability to freeze out requests made by surveillance systems, but they “rarely do so successfully” and “protections against unintended access are weak and easily defeated.” Some carriers have reportedly tried to plug this security gap. Nohl says he has consulted with cell carriers (he would not say which) on preventing surveillance companies from snooping. Still, it appears that whatever steps cell companies have taken to bolster customer privacy aren’t sufficient. After all, surveillance companies claim they can successfully track people more than 70 percent of the time, the paper notes.
Nate Cordozo, a staff attorney at the Electronic Frontier Foundation, says that if carriers don’t know their customer location data is being exploited, “there would be no violation of the privacy policy.” But if they are complicit, “then there’s a very good argument that there’s a violation of not only the privacy policies, but of the Electronic Communications Privacy Act in some contexts.” (The law prohibits eavesdropping on electronic information, which can include location data.) Companies could also be violating their privacy policies if they’re not taking sufficient steps to protect customer information, he notes.
Nohl contends that customers can be adequately protected from common surveillance tools if operators make a few changes to their systems, but not all are taking even these steps. “The negligence of many operators to protect from intrusive SS7 queries should be viewed as a privacy violation,” he says.