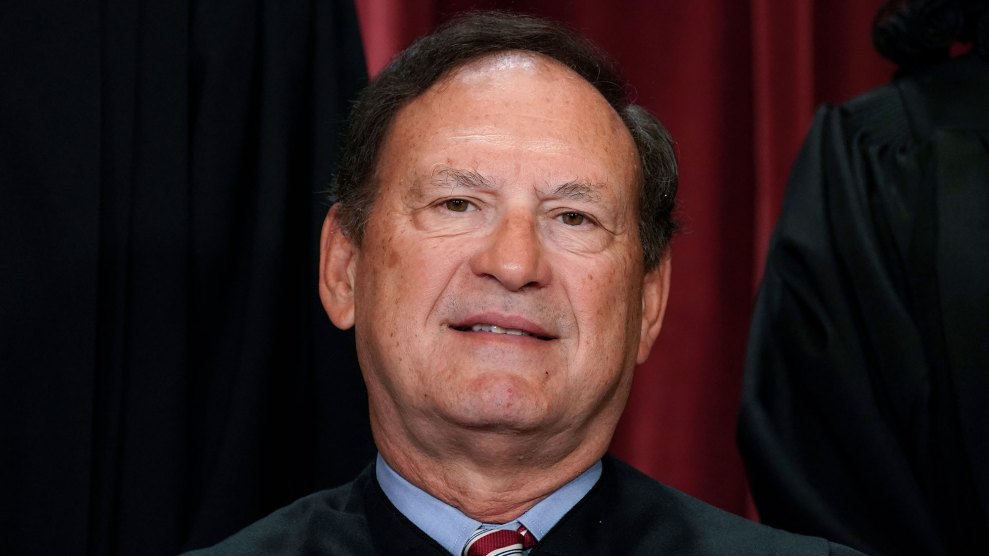
Andrew Harnik/AP
One time, I accidentally put a personal medical appointment on the public work calendar. Years ago, I tweeted something (very innocuous) from a brand account, intended for my own followers. The modern workplace requires vigilance (and numerous browsers and devices) to demarcate the strictly professional from the private. For you and me, co-mingling can feel inevitable, and a quick response can usually mop up most minor mishaps.
Now let’s look at the highest court in the land to see what kind of extra steps it might be taking to prevent lapses in judgement around sensitive documents.
Oh dear, reports CNN, in an exclusive article published this morning that paints a “detailed picture of yearslong lax internal procedures that could have endangered security” including the use of “personal email accounts for sensitive transmissions” by some of the justices themselves, instead of secure servers.
“This has been going on for years,” one former employee told CNN.
Let’s back up a moment. Feverish speculation about security lapses broke out when a draft opinion reversing Roe v. Wade was leaked to Politico, in May last year. An internal investigation began in earnest, led by Supreme Court Marshal Gail Curley. Who was the leaker? And what allowed for such a monumental breach?
The report issued by the court last month into what it described as “one of the worst breaches of trust in its history” failed to come up with a culprit.
CNN’s new reporting adds details to that investigation, including the haphazard use of “burn bags” intended for safe document destruction, which were reportedly left open and unattended; remote access that let employees print documents from any computer, making them harder to track; and the use of printers that didn’t produce security logs.
Apparently, part of the problem, according to one CNN source, was resistance from the justices themselves, who “were slow to adopt to the technology”, and employees who were too nervous to confront them.
According to one source quoted by CNN, the justices were “not masters of information security protocol.”
Read the full report here. And as always, people, change your passwords frequently and switch on two-factor authentication.