The excruciatingly narrow presidential contest in Florida four years ago left the nation eager to adopt a more reliable voting system — one that wouldn’t systematically disenfranchise swaths of voters or raise suspicions of tampering. The goal was to eliminate the crude machines, puzzling butterfly ballots, and hanging chads that cost thousands of voters their choice in 2000.
Nearly 10 million people are voting via computer this primary season. Most election officials in e-voting states hailed the outcome of Super Tuesday as a success for the largest test of electronic kiosks to date. Still, some of the six million California citizens who tried it found machines that didn’t boot up and coding software that failed to match votes with those who cast them. Some poll workers found that the programs they were called on to administer weren’t the ones they’d been trained for. Encoding problems even omitted propositions from some ballots.
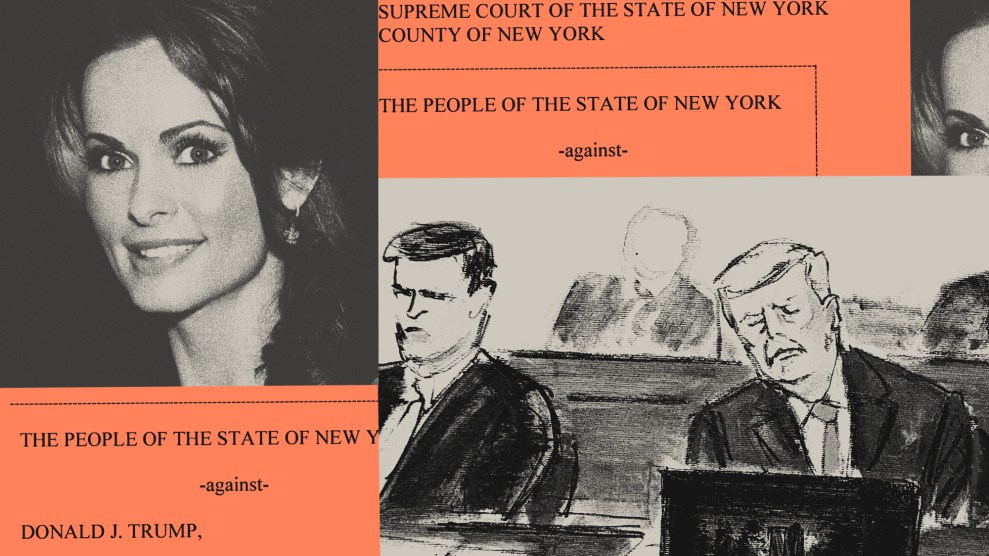
One in five U.S. voters will pick the president this November by pressing a button or computer screen. Votes will be cast in a hodgepodge of ways, most still using paper. Yet among digitized votes, if there are any virtual hanging chads, ballot-boxes stuffed, or votes wrongly hauled to the dumpster this time around, there will be no paper trail to prove it, or to divine voters’ real intentions.
Congress pledged $3.9 billion through the Help America Vote Act in 2002 for states to phase out punch-cards and lever voting booths and make voting easier for the elderly and disabled. States rushed to scrap paper ballots and set up computers for 2004 that would make voting as dummy-proof as withdrawing money from an ATM machine.
But it hasn’t quite worked out that way.
The effort to establish e-voting operates according to the same kind of dot-com era blind faith that prophesized paper-free workplaces. Studies show that offices use more paper than they did a decade ago; and electronic voting systems are proving the potential to be just as error-prone — if not more so — than the old way. Some Senate votes were double counted in South Dakota two years ago and in 2000, Florida machines added up a negative 16,000 votes for Gore.
Canada’s Globe and Mail elaborates:
The machines have already caused problems: In January, touch-screen machines used in a Florida county election failed to register 134 votes in a race won by just 12 ballots. And a number of recent studies have found security flaws that could allow hackers to break into machines and alter voting data undetected. One found that any high-school student with intermediate computer training would be able to use off-the-shelf equipment to forge cards used to initialize the voting machines and identify voters.
The overhaul might be happening too quickly to assure accuracy. Nor does it inspire confidence that the main provider of e-voting systems is a powerful backer of the Republican Party. A GOP fundraising letter from Diebold Election Systems CEO Walden O’Dell last year boasted that he’s “committed to helping Ohio deliver its electoral votes to the president next year.”
As Farhad Majoo of Salon put it, “What better way to deliver electoral votes for President Bush, some reasoned, than to control the equipment Americans use to cast their ballots?”
The strong smell of a Diebold conflict of interest came up after close Senate races in Georgia and Nebraska in 2002 prompted scrutiny of digital voting systems, especially by Democrats surprised by Republican victories. Accusations of dirty tricks are sure to surface again in the Bush-Kerry contest, especially if a Bush win again secures executive and legislative control by Republicans.
Adam Cohen of the New York Times, which set up a special section to track voting procedures, explains why many non-Republicans are paying special attention to the technology:
Totalitarian nations hold elections, but what sets democracies apart is offering real choices in elections. In recent years, contests for the House of Representatives and state legislatures have looked more and more like the Iraqi election in 2002, when Saddam Hussein claimed 100 percent of the vote for his re-election.
Diebold’s GOP support is especially key to note because as the corporation is private, so are its records. The equipment, software, and employees tallying votes are not subject to public scrutiny — so any suspicion of a skewed election can neither be proved or disproved
Activists last summer posted online thousands of internal Diebold emails suggesting that the company was hiding glitches in its systems. When Diebold demanded that Internet service providers delete the links, it was accused of stifling free speech. Diebold later backed down. Yet even government lacks the right to peek into this privately owned data to determine, say, the cause of the glitches in the most recent round of primaries.
It was California’s third election with touchscreen voting, but problems plagued 10 percent of machines in San Diego County. Faulty machines in the Bay Area’s Alameda County drove one in six voters away.
Kinks also bedeviled ballots in Georgia and Maryland. Georgia Green Party activists were urging people to cast early or absentee votes to get a paper ballot. Paper proved the only option for some Peach State voters when machines failed.However, human error was reportedly the major issue in Georgia due to voters filling out the wrong ballot or form.
Six voting machine makers formed a consortium in December to create a code of ethics and establish security standards. But is industry effort enough to guarantee a fair election? Unlikely.
Most new voting is done using Diebold machines, and there are major doubts about their effectiveness. Some experts warn that the Windows-based system is prone to viruses, worms and crashes. Computer security experts have described Diebold’s security about as foolproof as locking the front door but leaving a key in it.
The New York Times reports:
Proponents of the computer voting systems argue that the critics underestimate the degree to which good procedures can compensate for imperfect security. In Georgia, Mr. Williams said, individual precincts publish paper summaries of each machine’s results, providing an audit function.
“We don’t have to make the system a hundred percent secure,” he said. “What we have to do is make the security bar so high that anybody will say, `To heck with that.’ “
There is already recognition by some government officials that the bar for electronic voting should be higher. Owing to perceived security flaws in a system designed by Accenture (an offshoot of scandal-ridden Arthur Andersen), the Pentagon scrapped plans to expand the Secure Electronic Registration and Voting Experiment. This was an extension of the system that enabled overseas military personnel to vote in 2000.
Johns Hopkins and Rice University students scrutinized the source code of Diebold’s system and found glaring, sloppy errors. One researcher said, “unintended bugs are impossible to prevent and intentional back doors are impossible to detect.”
The most startling find was that it’s possible for someone to silently enter the system and edit votes without leaving a trace. This could be done, for example, using the vote-counting computer located in each e-voting county.
In a Salon interview last September, writer and activist Bev Harris described how anyone within reach of that terminal, “whether that’s the election supervisor, their assistants, the IT people, the janitor,” has election results at their fingertips:
“You don’t even need to break in. It will open right up and in you go. You can change the votes and you can overwrite the audit trail. It doesn’t keep any record of anything in the audit trail when you’re in this back door, but let’s say you went in the front door and you didn’t want to have anything you did there appear anywhere — you can then go in the backdoor and erase what you did.
…
” The other situation would be supposing someone gets in by either hacking the telephone system or by going backwards in through the Internet, because the Internet does connect to these GEMS computers, even though they deny it. A lot of the press watches election results come in on the Web and what they’re watching is actually being uploaded directly off the GEMS computer.”
Writing for Slate, Paul Boutin suggests using open-source software to prevent fraud. Otherwise:
The only sure check against an outlaw wacko programmer is an army of wacko programmers poring over every line of his work. There are also ways to verify that the booths themselves aren’t running tampered code. Instead of looking for Diebold’s ties to Dick Cheney, we should be watching that quiet new repairman.
After all the hubbub about a paper-free system, the next generation of computerized voting will likely output paper. California is demanding that within two years all voting kiosks print a paper receipt. A national bill demanding the same is in the House of Representatives, with strong backing from Democrats.
Cohen of the New York Times thinks that’s a good idea.
A healthy democracy must avoid even the appearance of corruption. The Georgia and Nebraska elections fail this test. Once voting software is certified, it should not be changed – not eight times, not once. A backup voting method should be available, so if electronic machines fail or are compromised shortly before an election, they can be dropped.
Votes must be counted by people universally perceived as impartial. States should not buy machines from companies that have ties to political parties, and recent company executives should not be running for elections on those machines.
Salon‘s Manjoo agrees:
An election has to be above suspicion, even above the suspicion of some of the most suspicious people in a democracy. Says California’s Tony Miller: “If people don’t have confidence in the voting systems being used, then they lose faith in the voting process itself.”