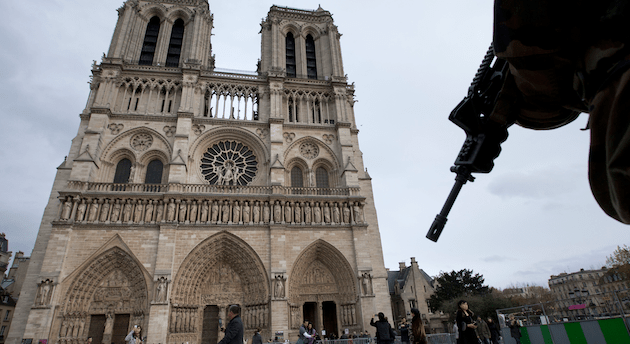
BrianAJackson/iStockPhoto
Syrian refugees aren’t the only ones feeling the backlash from the Paris attacks: Privacy advocates are worried that last week’s terrorist assault has created a climate that threatens digital privacy in the United States and elsewhere.
The horrific attacks led to calls for the US government to roll back surveillance reform and digital privacy protections enacted following leaks by former NSA contractor Edward Snowden. Some politicians, including presidential candidates Marco Rubio and Jeb Bush and Republican members of Congress, argue that the United States currently lacks the tools to keep tabs on terrorists when they use phones or online communications. That echoes the argument FBI director James Comey has made for months: Terrorists are “going dark,” he says, and the FBI and other agencies are losing the ability to track them. But privacy rights advocates fear this post-Paris push threatens to undermine important reforms, with little evidence that the proposed changes would prevent attacks.
“It’s predictable but a bit sickening,” says Elizabeth Goitein, the co-director of the Brennan Center for Justice’s Liberty and National Security Program. “These attacks were just heartbreaking, and people are understandably anxious for their government to do more to protect them. But what we’re seeing is that some officials and policymakers are really exploiting…people’s grief and fear to promote expansions of power that they know full well would not have prevented the terrorist attacks.”
Here’s what lawmakers and politicians have proposed:
Encrypted communications: Law enforcement officials, led by Comey, have claimed for months that ISIS operatives are using encrypted communications—including popular messaging services such as WhatsApp and Telegram—to make themselves virtually invisible to intelligence and law enforcement agencies. “Encryption threatens to lead us all to a very, very dark place,” he said during a speech in Oct. 2014, warning that the use of impenetrable encryption might make it more likely that a terrorist attack would succeed. Comey and others, including CIA Director John Brennan, sounded the encryption alarm again after the Paris attacks. But it turned out the attackers were likely using plain old text messages, which are unencrypted, to communicate.
Comey proposes that tech companies build “backdoors” into their encryption so police or intelligence agencies can read messages. But tech companies and encryption experts say any hole in the encryption can be used by anyone, from the FBI to cybercriminals to foreign governments. “You can’t have a backdoor in the software, because you can’t have a backdoor that’s only for the good guys,” said Apple CEO Tim Cook last month. A lobbying group representing Apple, Google, and other major tech firms also came out against backdoors on Thursday. “After a horrific tragedy like the Paris attacks, we naturally search for solutions: weakening encryption is not a solution,” Dean Garfield, president of the Information Technology Industry Council, said to Reuters.
Amie Stepanovich, the US policy manager for the digital privacy group Access, points out that intelligence agencies reportedly have ways to break into individual devices, rather than weakening encryption used by millions of internet users. “In Europe, a lot of intelligence and law enforcement agencies believe that they can hack into user devices if they need to get information,” she says. “We have to take those into account when we’re talking about proposals that would impact the safety and security of everybody who uses encryption.”
The White House said last month that it wouldn’t push for a law forcing tech companies to build backdoors into their products, but Sen. John McCain (R-Ariz.) said on Tuesday that he would hold hearings on backdoors and start working on a law requiring them.
CALEA: A related, if somewhat more obscure issue, is the Communications Assistance for Law Enforcement Act, or CALEA. The law requires phone systems, internet providers, and internet calling services to be tappable so the police can access them with warrants. Other forms of internet communications and messaging have been exempted from the law thus far. But that could soon change.
Tom Wheeler, chairman of the Federal Communications Commission, suggested on Tuesday at a House hearing that Congress could update the law to include internet services after Rep. Joe Baron (R-Texas) asked what could be done to give the government more power to shut down websites or networks potentially used by terrorists. His testimony was based in part on another false rumor that the Paris attackers used PlayStation 4 game consoles to secretly communicate with each other. “They’re using the internet in an extremely offensive, inappropriate way against us, and we ought to be able to make it, at a minimum, much more difficult and hopefully absolutely shut it down,” Barton said at the hearing.
Stepanovich and other privacy advocates contend that changing CALEA is simply another way of requiring backdoors, but perhaps on a much larger scale that would permit the government to shut down full websites or social media networks.
NSA reform: Congress passed the USA Freedom Act in June, a law that barred the NSA from sucking up the user records—or “metadata”—of phone calls en masse. Under the new law, phone companies will keep the data and the government will have to seek permission from a judge to get specific records. Privacy groups and pro-reform members of Congress considered the end of the NSA’s bulk metadata collection the “most significant win for privacy rights in a decade,” in the words of Sen. Ron Wyden (D-Ore.). But with only nine days to go until the program ends, some lawmakers are trying to bring it back.
Sen. Tom Cotton (R-Ark.), one of the Senate’s most hardline hawks, introduced a bill on Tuesday to delay the termination of the metadata program for more than a year. “We should allow the intelligence community to do their job and provide them with the tools they need to keep us safe,” he said in a statement. Some GOP presidential candidates are joining the chorus, pushing to undo surveillance reform. Sen. Marco Rubio (R-Fla.) backs Cotton’s bill, and former Florida Gov. Jeb Bush also wants to reinstate bulk collection.
Privacy advocates say encryption and surveillance reform have no connection to how the Paris attacks were able to be planned, and that weakening privacy protections would be unlikely to stop future attacks. “There really is no way to see rolling back USA Freedom as a potential solution against any sort of future attacks similar to what we recently saw in Paris and Beirut,” Stepanovich says. They also point out that the reforms were broadly popular in the wake of the Snowden leaks and the increased attention on government surveillance. “It’s important to remember that when those reforms passed, they passed overwhelmingly and they were supported by a large subset of the population,” says Neema Singh Guliani, a legislative counsel at the American Civil Liberties Union.
Privacy advocates note that the odds of increased surveillance measures are high in the aftermath of any attack. “In the past that’s been a successful strategy, so I certainly take it seriously,” says Goitein of the Brennan Center. Stepanovich cites the Patriot Act as a cautionary tale: “You have these reactionary responses from people who really want to do something, and they’re trying to figure out what they can do quickly. We saw in the wake of 9/11 that lawmakers are able to use that to elbow through expanded authorities and provisions.”
Singh Guliani cautioned that if updated policies are needed, so is more extensive debate about which ones to adopt: “It’s important that we make sure that whatever policy we’re pursuing is based on facts, based on reasoned debate, based on public input—not based on just the moment.”