People who live near chemical plants can no longer go online and find out which hazardous materials are stored near their home. Air travelers can no longer see Federal Aviation Administration records on airport-security violations. Journalists and elected officials no longer have access to a string of reports pinpointing weaknesses in the nation’s antiterrorism defenses.
When the federal government scrambled to remove vast amounts of information from official libraries and websites in the wake of September 11, most assumed that access would be restored after officials had a chance to carefully evaluate security risks. But instead, many observers now say, the administration has used a string of laws and executive orders to reverse a decades-long trend toward government openness. The new measures are so broad, critics warn, it’s impossible to say whether officials are protecting national security or simply expanding their power to operate without public scrutiny. “An iron veil is descending over the executive branch,” warns Rep. Dan Burton (R-Ind.), chairman of the House Committee on Government Reform.
The first of the new secrecy measures was rushed through Congress in October 2001 as part of the USA Patriot Act, which gave law-enforcement agencies the authority to search homes and businesses without a warrant (a practice known as “sneak and peek”) and to secretly track an individual’s Internet surfing, library records, and book purchases. When the House Judiciary Committee asked last June how many times the FBI had used each of the new powers — many of which were taken away from the bureau in the past because of abuses — the Justice Department said that information was classified. “Their attitude seems to be that even Congress isn’t entitled to know how they’re using the authority that Congress gave them,” says outgoing Rep. Bob Barr (R-Ga.).
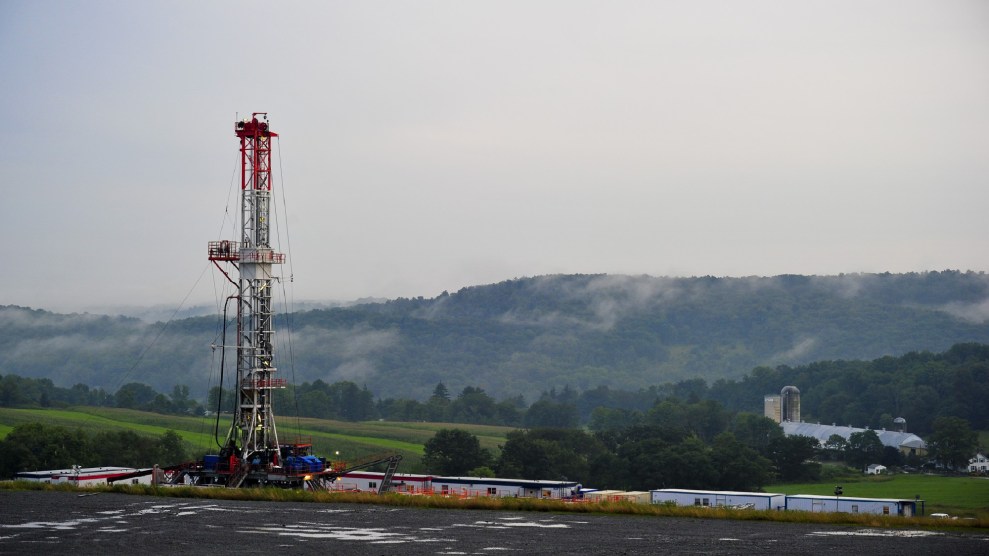
The push toward secrecy has extended far beyond law enforcement. Under a new policy restricting access to “sensitive but unclassified” information, agencies have made it harder for the public to see records that are often used by health and safety advocates and that industry has long sought to keep secret. The EPA, for instance, now limits access to the “risk management plans” that companies must file to inform communities what is being done to prevent toxic chemical accidents, and the Federal Energy Regulatory Commission has withdrawn information on hazardous materials stored at power plants.
In some cases, officials are withholding information that could embarrass government agencies or businesses. Last summer, the Department of Agriculture tried to suppress a National Academy of Sciences study that revealed no government secrets but warned that terrorism using foreign pests or pathogens could “pose a major threat to U.S. agriculture.” (The academy went ahead and published the report on its own.) The Agency for Toxic Substances and Disease Registry no longer allows online access to a report that characterizes security at chemical plants as “fair to very poor.” The Nuclear Regulatory Commission has restricted access to two reports — one of which had been available for 20 years — that suggest that nuclear power plants are not adequately protected against airplane crashes. And at the EPA last summer, officials, arguing that disclosing information about new appointees constituted a security risk, censored résumés to remove information on education levels and job experience.
Soon, even private companies may be able to seal off information they don’t want the public to see — simply by sending it to the federal government. Attorney General John Ashcroft has singled out “sensitive business information” as one of the categories federal officials should shield from Freedom of Information Act requests. And under legislation creating the Department of Homeland Security, most information provided by business — on anything from software security problems to toxic spills — will be exempted from public-access laws. For example, notes Natural Resources Defense Council attorney Jon Devine, if an improperly stored load of hazardous material were to explode at a chemical plant, information on the substances involved — and even evidence of negligent storage — could be off-limits to firefighters, local investigators, and the victims themselves. “The only thing the government can use the information for,” Devine says, “is to determine whether they need more security. But they can’t force the company to do anything about it.”
Across the country, state officials are following the federal government’s lead in closing off public records. Pennsylvania has dismantled a database with environmental information about mines and soil conditions. Iowa has classified architectural information on school buildings. And several states, including Louisiana, have passed anti-terrorism laws that allow local police to keep secret any information gathered in connection with terrorism investigations. Since local police have no jurisdiction over foreign terrorists, notes Joe Cook of the Louisiana Civil Liberties Union, the provisions most likely will be used to conceal files on political activists. “It puts in jeopardy groups that have no intention of being involved in terrorism,” he says.
The full implications of these and other measures — including additional secrecy provisions tucked into November’s homeland security legislation — have yet to emerge as officials begin to make full use of their powers. “It’s only been one year,” says David Cole, a professor of law at Georgetown University. “These laws lie around like loaded guns that law enforcement can pick up whenever they please. They don’t pick them all up at once.”